
Earn your graduate degree at St. Mary’s University
Thank you so much for your interest in Graduate Studies at St. Mary’s University. We’re thrilled that you’re considering joining our history of academic excellence at the graduate or doctoral level. Wherever you are in your application journey, please feel free to reach out to the Office of Graduate Admission with any questions.
Ready to apply?
It is free and easy to apply to St. Mary’s University using our online application. Use the button below to get started today.


Founded in Marianist Values
St. Mary’s University educates ethical leaders for the common good. We are committed to helping you find a profession that aligns with your personal values and educational background so that you may find more than just a career — you’ll find your true calling.
A History of Academic Excellence
We are committed to providing students with experiential learning opportunities that inform their development of faith and vocation, their understanding of justice and the common good, and their journey to becoming leaders in our local, national and global communities.
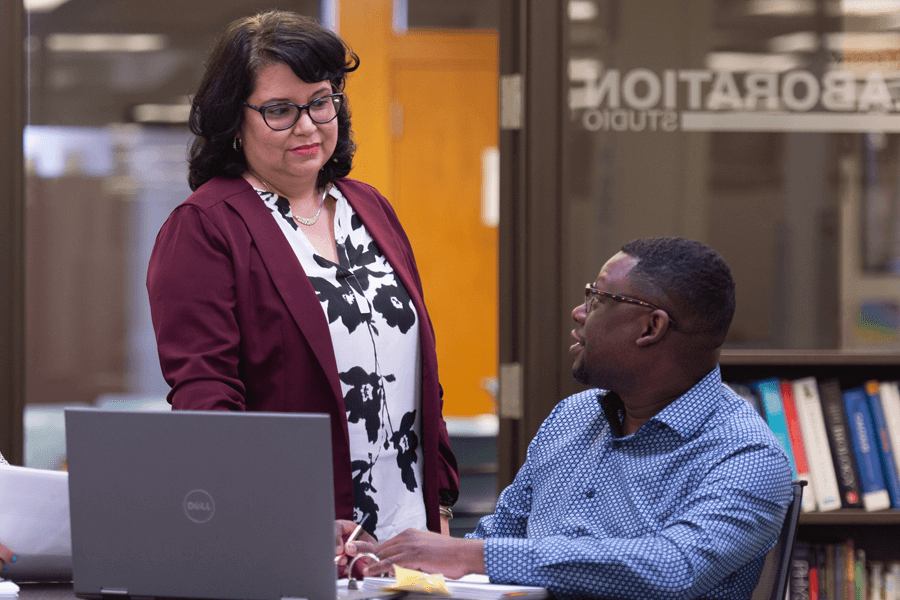
Chat with a Graduate Admission Counselor
The Office of Graduate Admission offers prospective graduate students the ability to meet with a Graduate Admission Counselor to learn more about our academic programs, admission, financial aid options and our amazing faculty. Please submit your request 24 hours in advance of your preferred date and time.
Prospective graduate students can schedule a one-on-one or coffee chat with a Gradaute Admission Counselor.
Featured Graduate Programs

Online MBA for Professionals
- Master of Business Administration https://www.stmarytx.edu/admission/graduate-admission/ https://www.stmarytx.edu/wp-content/uploads/2017/01/reinbolt-wide.jpg

Master of Arts in Clinical Mental Health Counseling
- Master of Arts https://www.stmarytx.edu/admission/graduate-admission/ https://www.stmarytx.edu/wp-content/uploads/2017/01/reinbolt-wide.jpg

Master of Public Administration
- Master of Public Administration https://www.stmarytx.edu/admission/graduate-admission/ https://www.stmarytx.edu/wp-content/uploads/2017/01/reinbolt-wide.jpg

Doctor of Philosophy in Counselor Education and Supervision
- Doctorate https://www.stmarytx.edu/admission/graduate-admission/ https://www.stmarytx.edu/wp-content/uploads/2017/01/reinbolt-wide.jpg

Master of Science in Computer Science
- Master of Science https://www.stmarytx.edu/admission/graduate-admission/ https://www.stmarytx.edu/wp-content/uploads/2017/01/reinbolt-wide.jpg

Master of Science in Industrial / Organizational Psychology
- Master of Science https://www.stmarytx.edu/admission/graduate-admission/ https://www.stmarytx.edu/wp-content/uploads/2017/01/reinbolt-wide.jpg

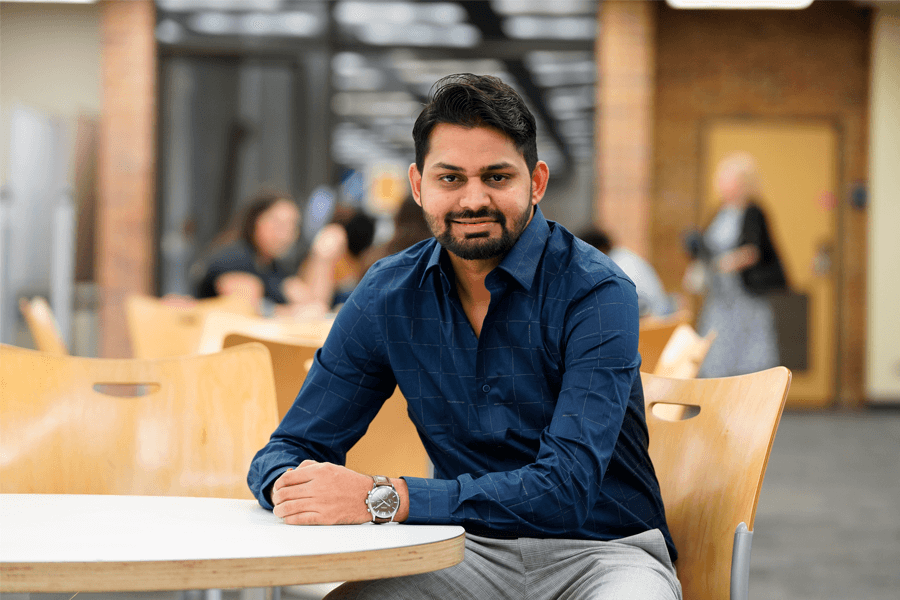
The philosophy of St. Mary’s University, being welcoming to all, drew me in. The University has a very diverse student population. Some are Catholic, and some are not. Everyone gets treated the same and shares their different points of view.”
Raul Rodriguez (M.B.A. ’22)
Graduate Admission Requirements
How do I apply to graduate programs at St. Mary’s?
All programs require an official degree-granting transcript. International applicants must send an international credential evaluation from a NACES member agency. The GRE/GMAT is optional unless otherwise noted. Requirements are subject to change and additional materials may be required. Contact your program director or Graduate Admission for details.
| Program | Letter(s) of Recommendation | Statement of Purpose | Resume/CV | GRE/GMAT | Start Term* |
|---|---|---|---|---|---|
| MBA for Professionals – Online | 2 | ✓ | ✓ | Any |
Greehey School of Business Requirements
| Program | Letter(s) of Recommendation | Statement of Purpose | Resume/CV | GRE/GMAT | Start Term* |
|---|---|---|---|---|---|
| Certificate Biblical Studies | 1 | ✓ | Any | ||
| Certificate Community-based Assessment and Evaluation | ✓ | ✓ | Any | ||
| Certificate Digital Communication | ✓ | ||||
| Certificate Dual Credit Teaching English, Literature and Language | 1 | Any | |||
| Certificate Dual Credit Teaching U.S. History | Any | ||||
| Certificate Dual Credit Teaching in Psychology | 1 | Any | |||
| Certificate Public Communication, Public Policy, and Public Leadership | ✓ | ✓ | Any | ||
| Certificate Theology | 1 | ✓ | Any | ||
| Certificate U.S. Public History | Any | ||||
| Clinical Mental Health Counseling | 2 | ✓ | Any | ||
| Communication Studies | 2 | ✓ | Any | ||
| Counselor Education and Supervision (Doctoral) | 3 | ✓ | ✓ | Fall | |
| English Literature and Language | 2 | ✓ | Any | ||
| International Relations – Security Policy | 2 | ✓ | Any | ||
| International Relations – Sustainability Development and Conflict Transformation | 2 | ✓ | Any | ||
| Public Administration | 2 | ✓ | ✓ | Any | |
| Public History | Any | ||||
| Theology | 2 | ✓ | Any | ||
| Industrial/Organizational Psychology | Reference list required | ✓ | ✓ | ✓ | Fall |
| Program Evaluation | ✓ | Any |
College of arts, humanities and social sciences requirements
| Program | Letter(s) of Recommendation | Statement of Purpose | Resume/CV | GRE/GMAT | Start Term* |
|---|---|---|---|---|---|
| Certificate Cyber Security | ✓ | ✓ | Any | ||
| Certificate Educational Computer Gaming | ✓ | ✓ | Any | ||
| Certificate Construction Management | ✓ | ✓ | Fall or Spring | ||
| Certificate Software Engineering – Online | ✓ | ✓ | Any | ||
| Electrical and Computer Engineering | 2 | ✓ | ✓ | Any | |
| Computer Information System | 2 | ✓ | ✓ | Any | |
| Computer Science | 2 | ✓ | ✓ | Any | |
| Cyber Security | 2 | ✓ | ✓ | Any | |
| Industrial Engineering and Management | 2 | ✓ | ✓ | Any | |
| Software Engineering – Online | 2 | ✓ | ✓ | Any |
School of Science, Engineering and Technology Requirements
- Minimum of 6.0 on IELTS for all graduate programs (except MBA: applicants require 6.5 on IELTS)
- Minimum of 80 on TOEFL for all graduate programs (except MBA: applicants require 87 on TOEFL )
- Minimum of 115 on Duolingo English Test
International Students Language Proficiency Requirements
Important Application Dates
Graduate Domestic Application Deadlines
Academic Term Application Priority Deadline Fall Semester (Aug. to Dec.) July 1 Spring Semester (Jan. to May) Nov. 15 Summer Semester (begins late May/early June) Apr. 1 Graduate International Application Deadlines
Academic Term Application Priority Deadline (if you are outside the U.S.) Application Priority Deadline (if you are inside the U.S.) Fall Semester (Aug. to Dec.) May 1 June 15 Spring Semester (Jan. to May) Oct. 1 Nov. 15
Get Personalized Academic Support
The Graduate Center for Excellence is a collaborative learning space designed exclusively for St. Mary’s master’s and doctoral students to collaborate with classmates and students from other disciplines.
Take a closer look. Preview the graduate experience at St. Mary’s!
Contact Us
Office of Graduate Admission
Chaminade Tower
210-436-3126
graduate@stmarytx.edu
